Bitcoin Explainers
Visual guides and interactive explanations to help you understand Bitcoin concepts through carefully crafted slides and diagrams.
Explore Topics (16)
CPFP - Child Pays For Parent
Understanding how child transactions can accelerate parent transactions through higher fees
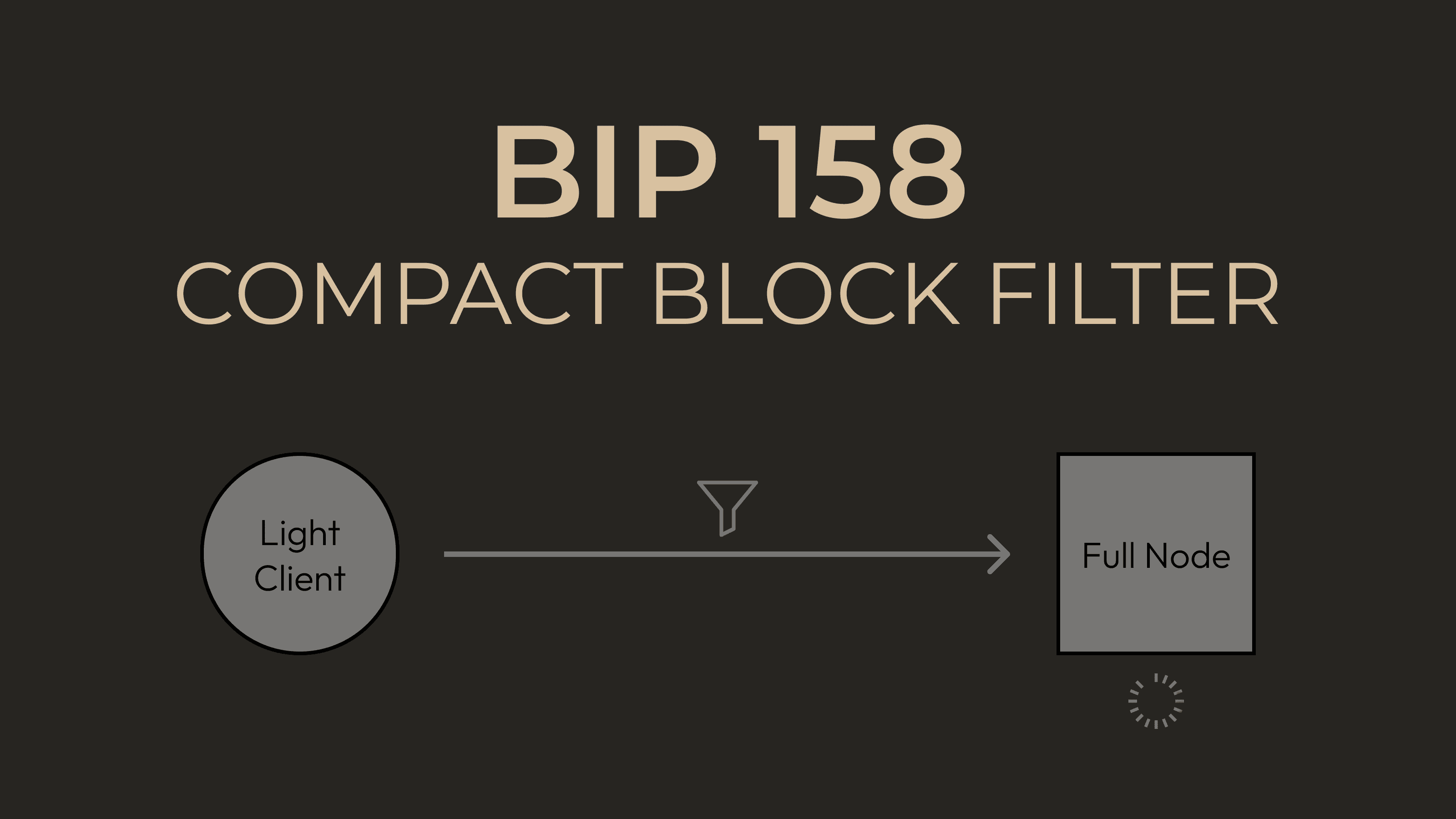
BIP-158: Compact Block Filters
Understanding Bitcoin's compact block filters for lightweight client privacy and efficiency
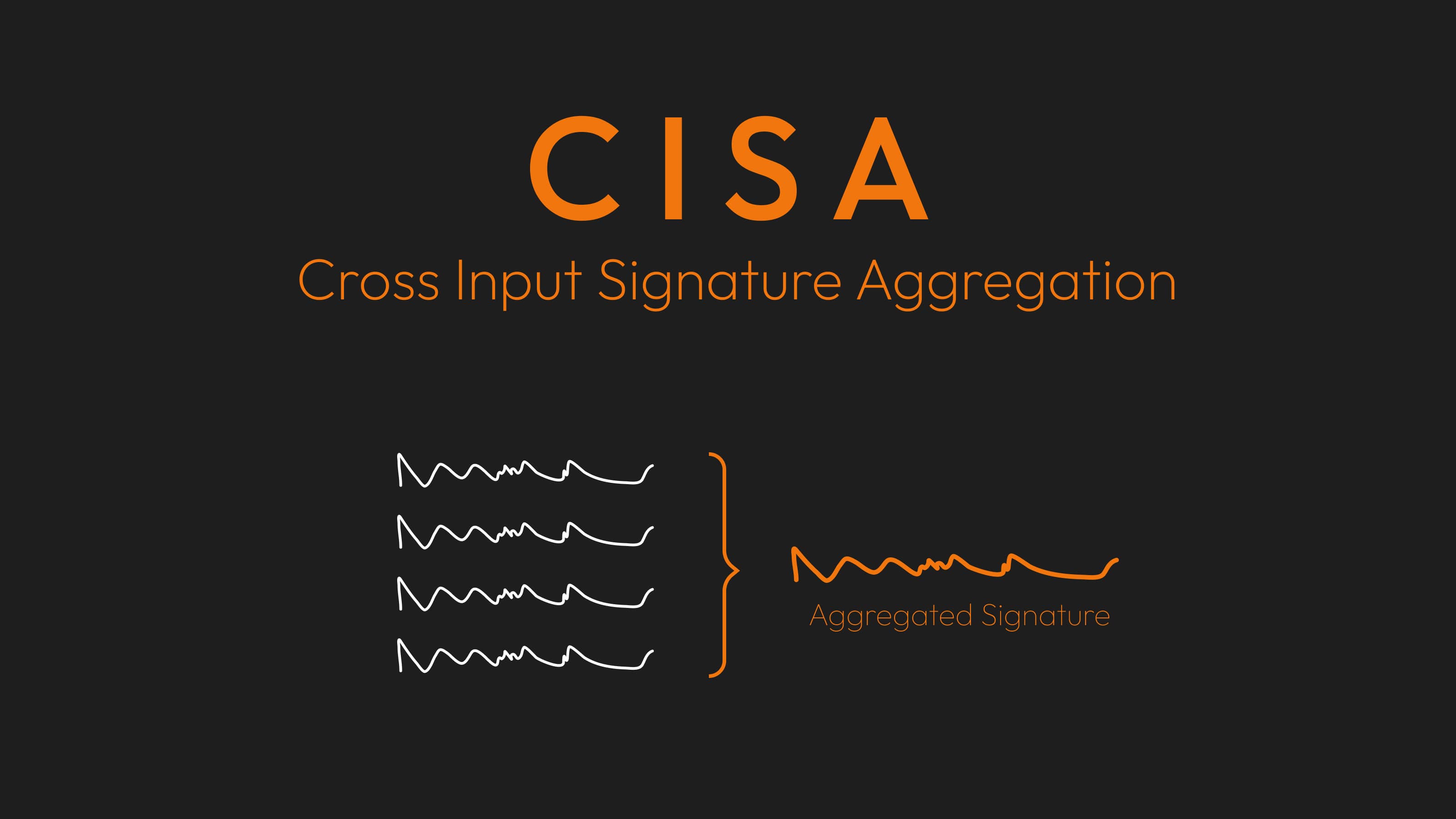
CISA: Cross-Input Signature Aggregation
Understanding how CISA can improve Bitcoin transaction efficiency and privacy through signature aggregation
Commit-Delay-Reveal Protocol
Understanding commitment schemes and reveal protocols in cryptographic systems
Common Input Ownership Heuristic
Understanding how blockchain analysis uses input clustering to trace Bitcoin transactions

Steal-Burn Dilemma
Understanding the economic security dilemma in cryptocurrency systems
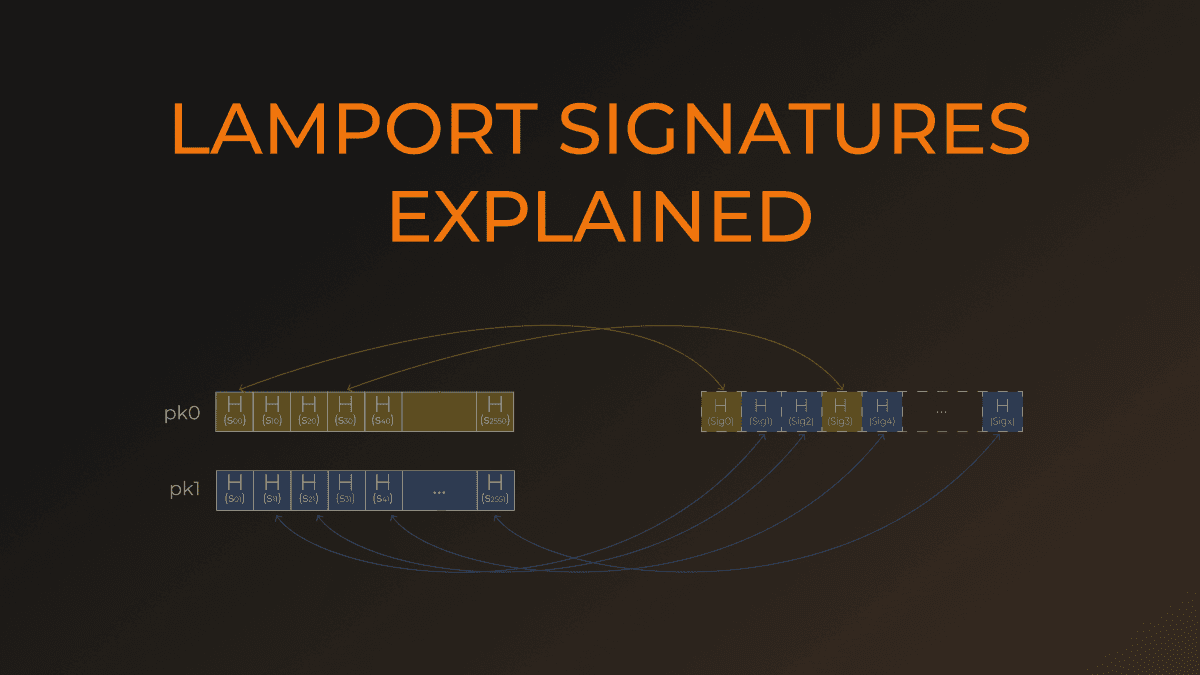
Lamport Signatures
Understanding one-time quantum-resistant digital signature schemes
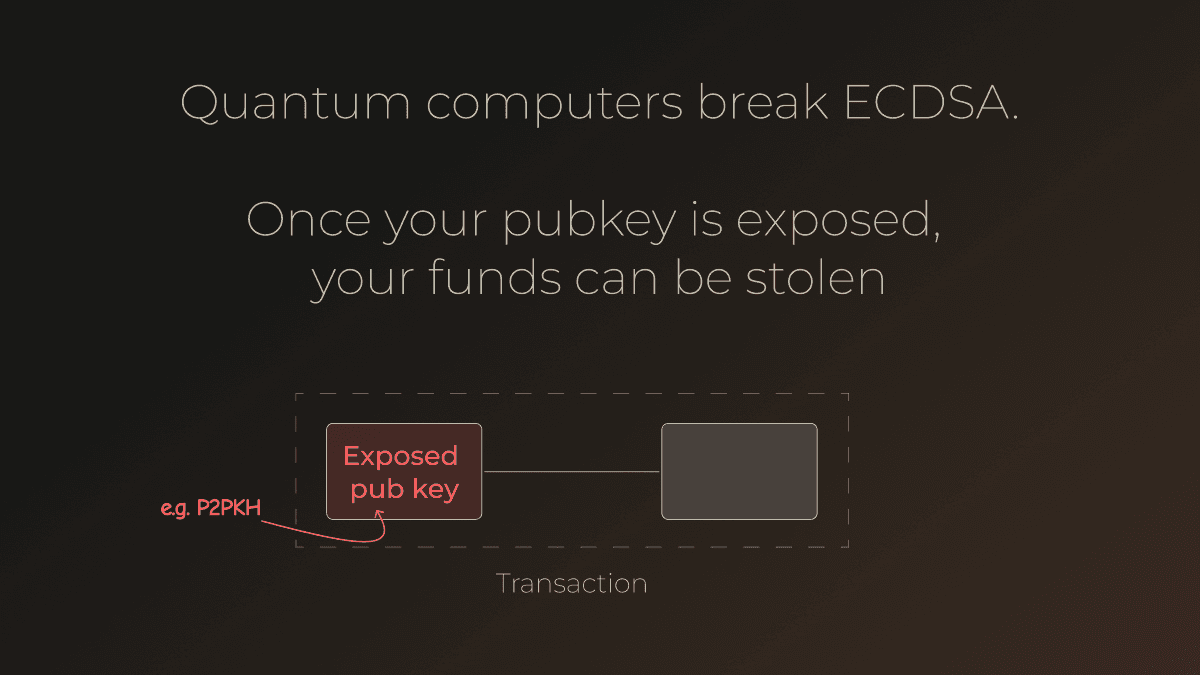
Quantum Computer Threats
Understanding how quantum computing poses threats to current cryptographic systems

SPHINCS+
Understanding the SPHINCS+ post-quantum digital signature scheme
Long & Short Range Attacks
Understanding long-range and short-range attacks on blockchain networks
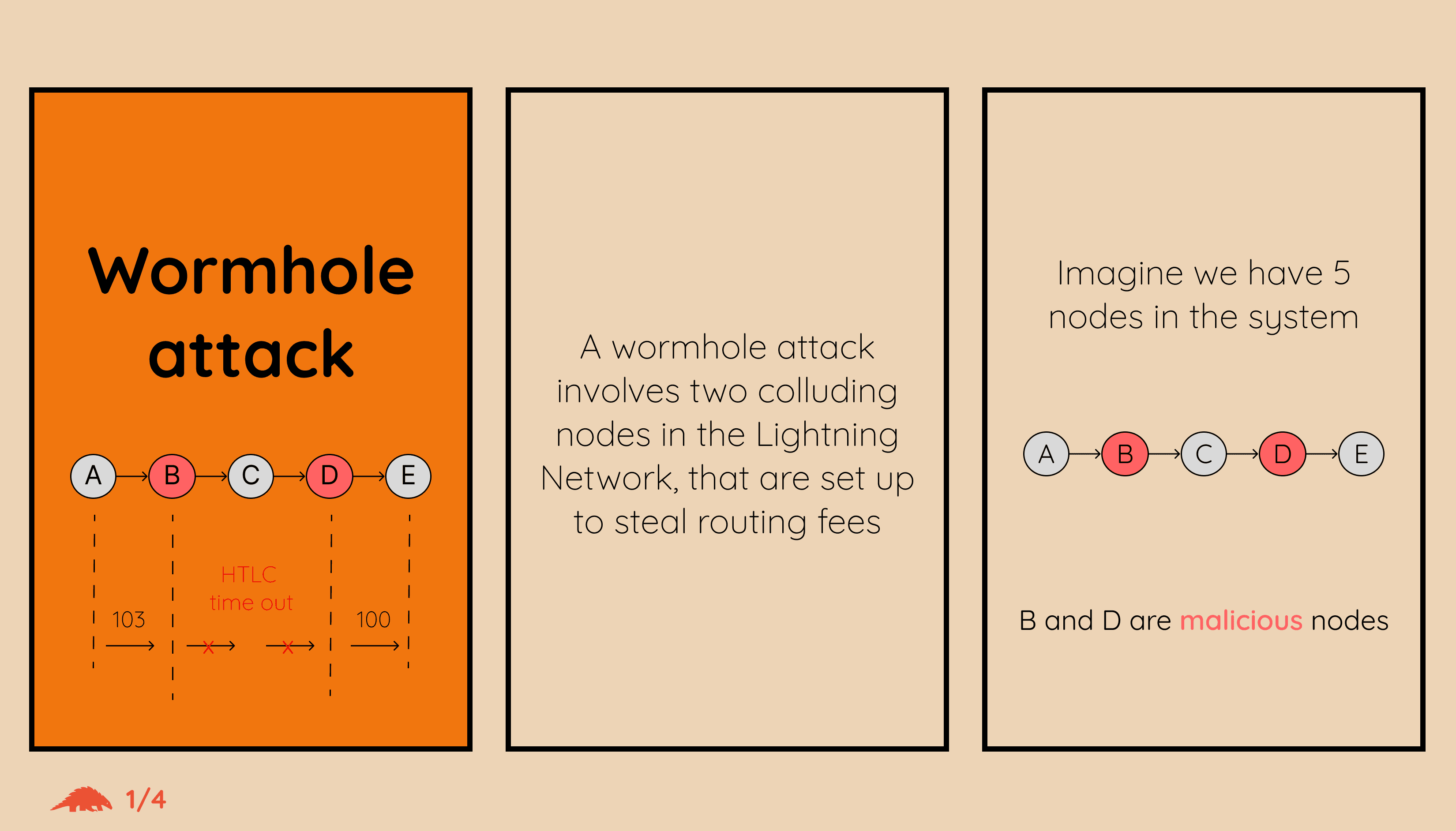
Wormhole Attack
How two colluding nodes in the Lightning Network can steal routing fees by bypassing intermediate nodes using the HTLC pre-image
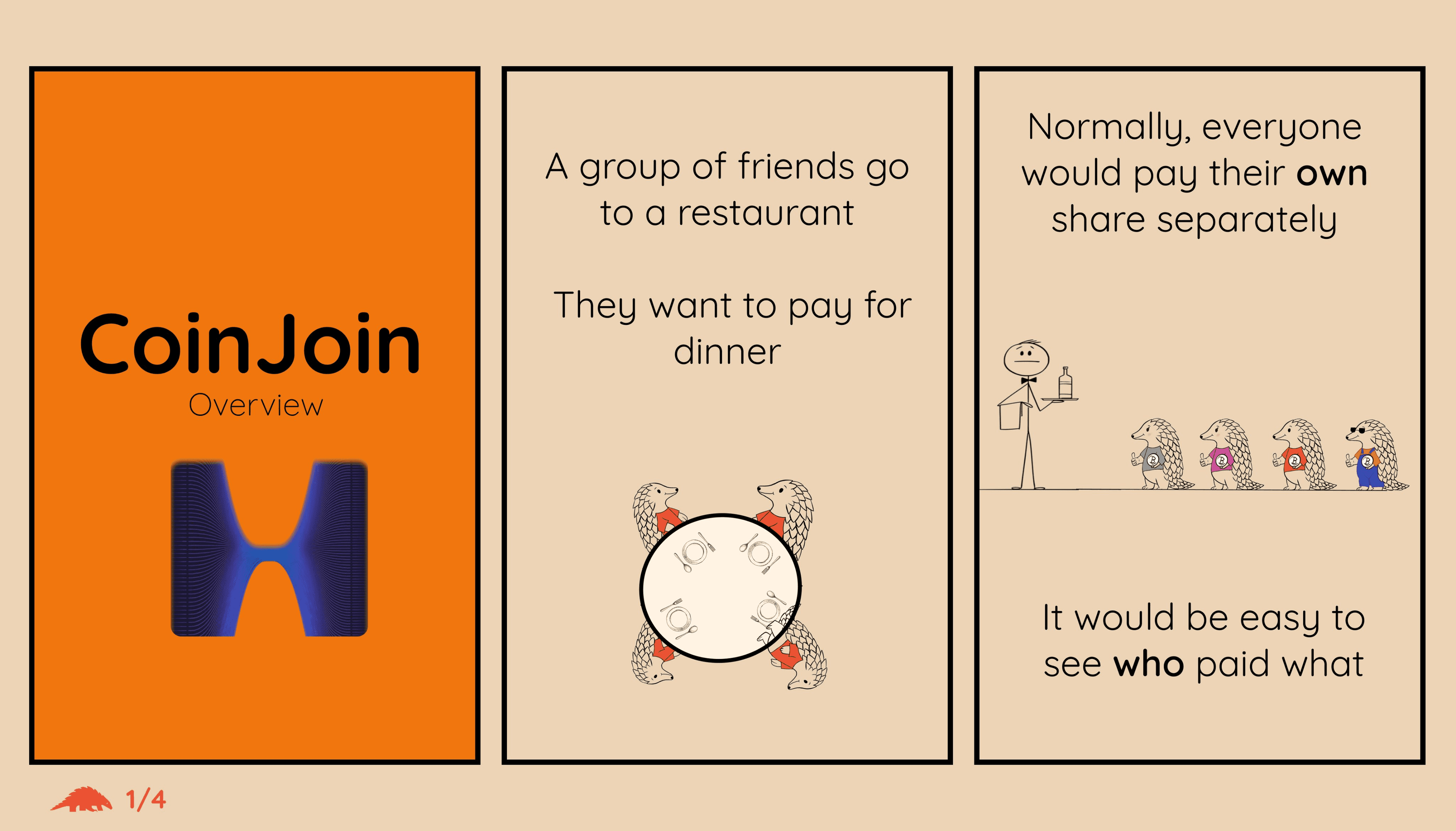
CoinJoin
How CoinJoin combines multiple Bitcoin transactions into one to enhance privacy by obscuring the link between inputs and outputs
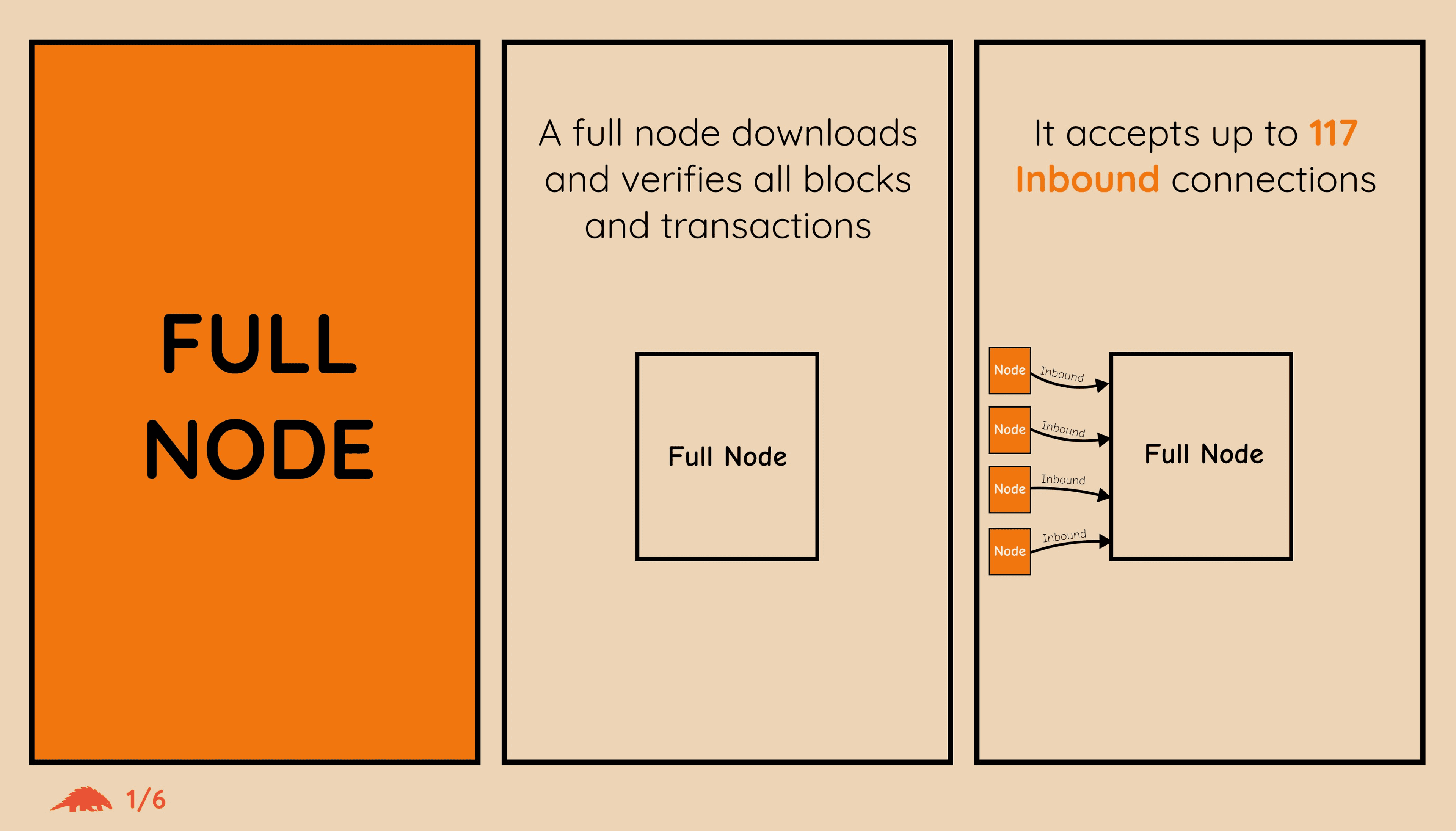
Full Node
What a Bitcoin full node is, why it matters, and how it enforces the rules of the Bitcoin network without trusting anyone
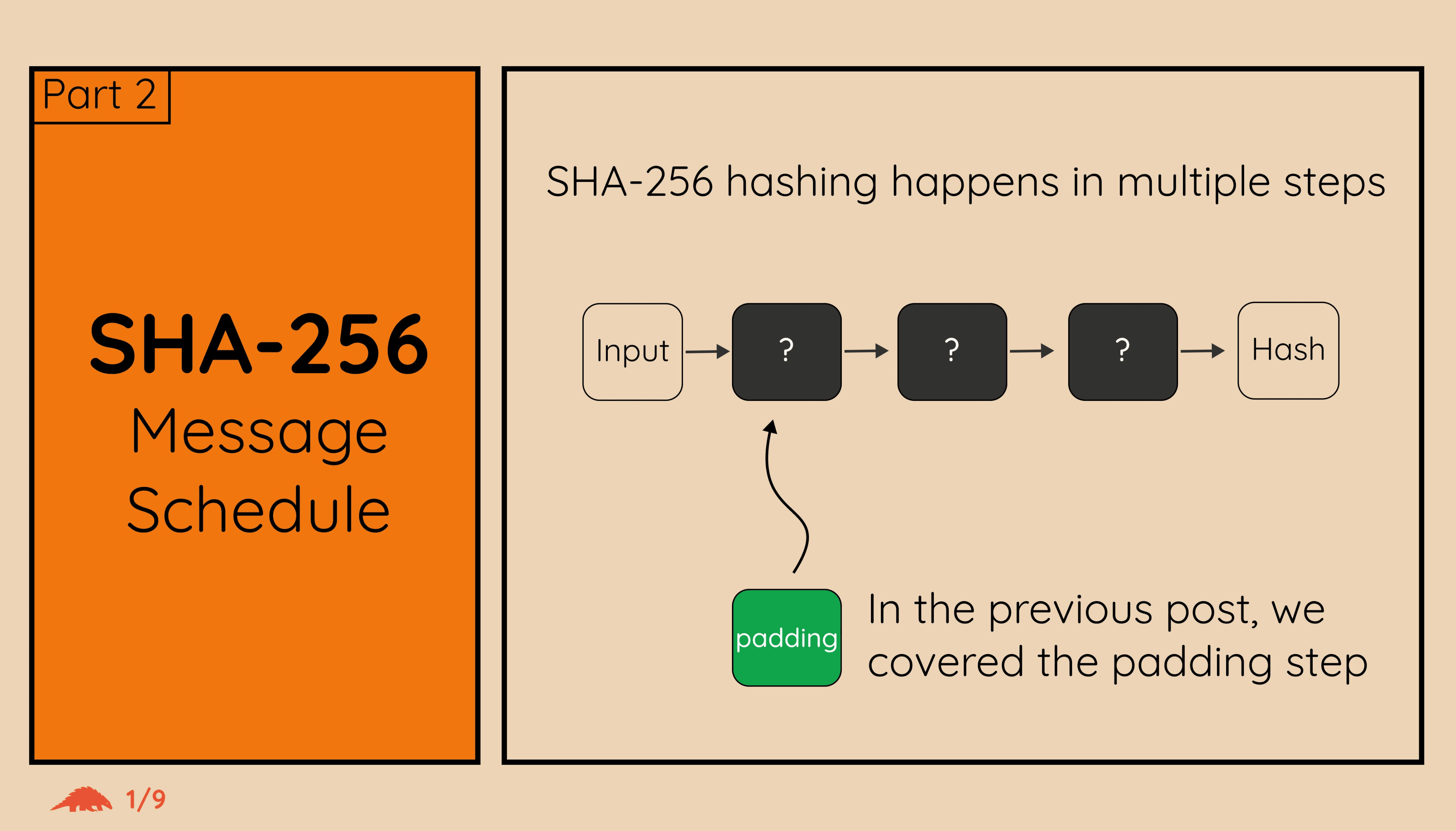
SHA256 Message Schedule
A deep dive into the SHA256 message schedule — how the 16 input words are expanded into 64 words used in the compression function
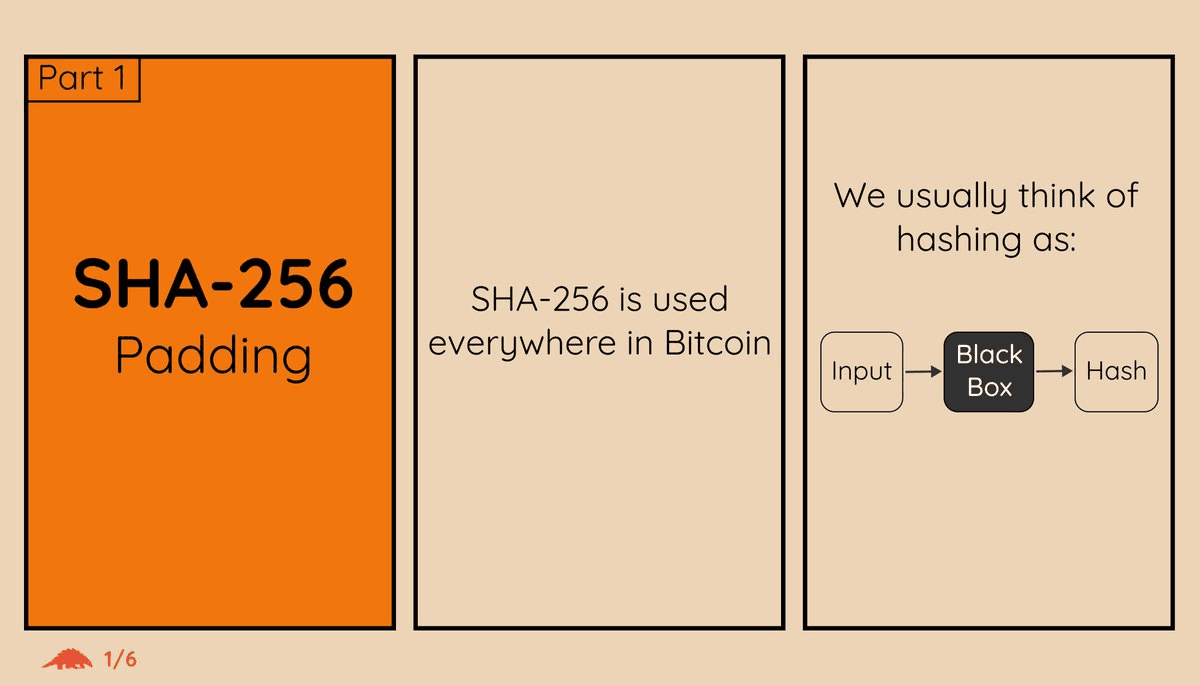
SHA256 Padding
How SHA256 pads messages to a multiple of 512 bits before hashing, including the length encoding
Transaction Pinning
How transaction pinning attacks exploit mempool rules to prevent fee bumping, and why this matters for Lightning Network security
